New Blog
Friday, January 16, 2009
Rather than resurrecting this dinosaur, all new posts will be on my new Wordpress blog, "Of Bytes and Badges." Feel free to drop me a line there and let me know you've made the switch, and welcome to a badly-needed update and overhaul!
- David Oxley
posted by David @ 9:00 PM,
,
![]()
Told You So -- ErrorSafe Pop-Ups Served via Ruckus
Thursday, August 16, 2007
Well, listening to my morning dose of Sara Groves, I saw a familiar pop-up that I'd called coming a short while ago (look towards the end):
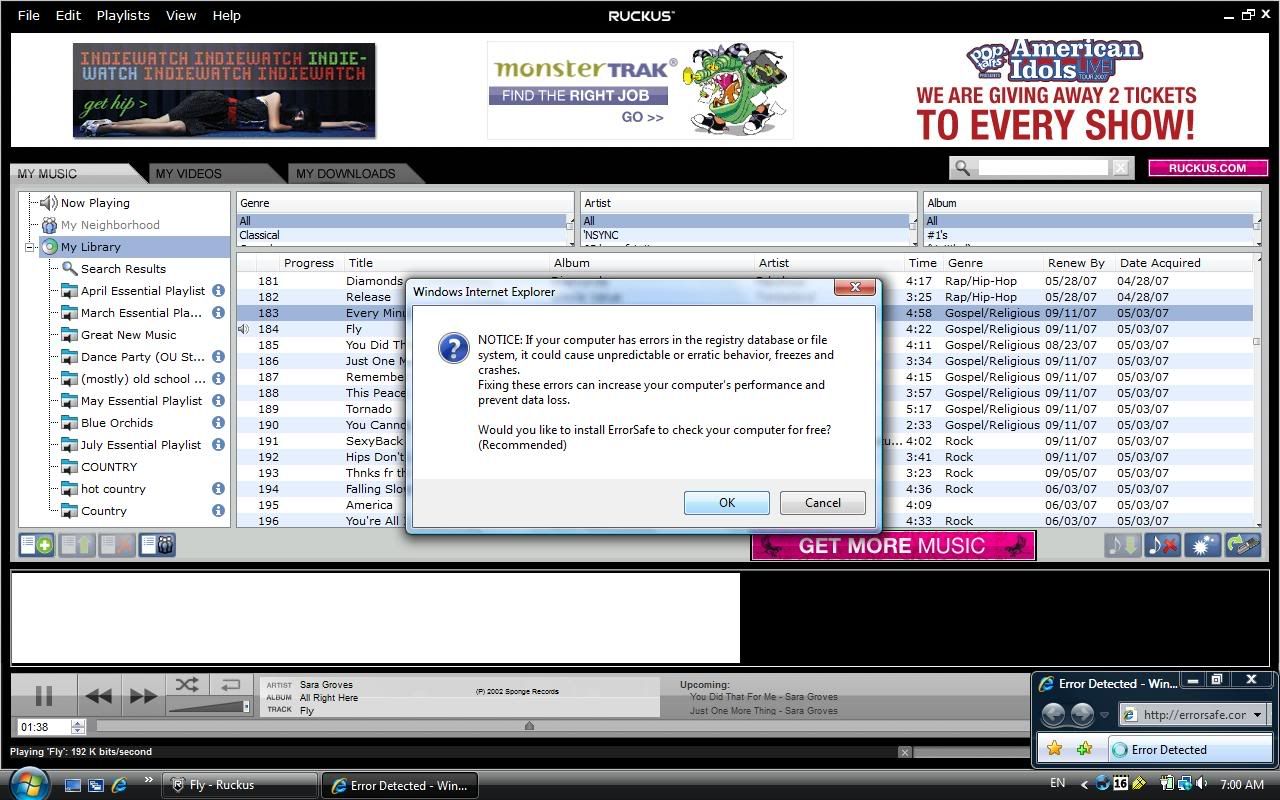
That's right, ErrorSafe! (If you're not familiar with the rogue AV/registry cleaner/etc. scene, such programs claim that there are a bunch of problems that need to be fixed...for a fee. They install without user consent, and have little or no real functionality). Clicking anywhere on the message (NOTE: even on the red "X" in the corner) loads the ErrorSafe install page in IE7:
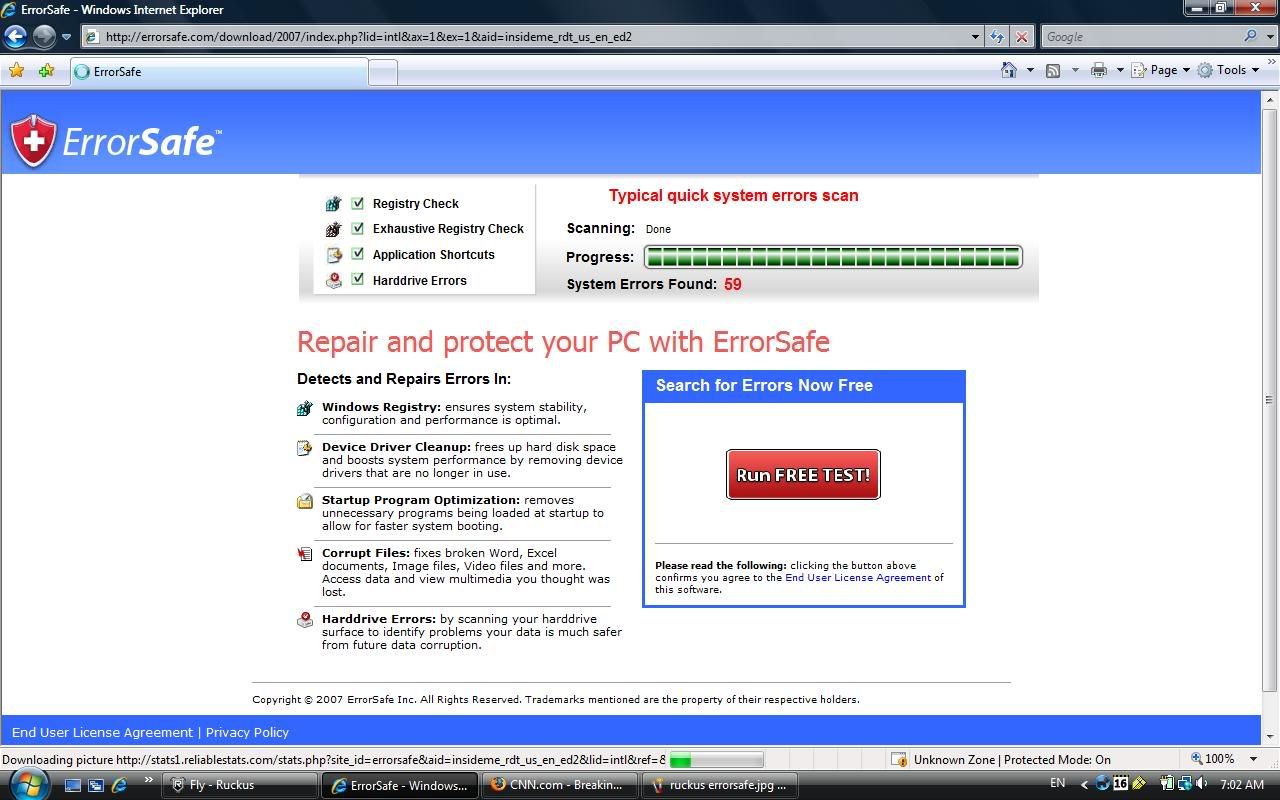
...and not only that, the page then attempts to install the rogue program without user consent (in this case, Symantec caught the .cab file while it was still in the Temporary Internet Files):
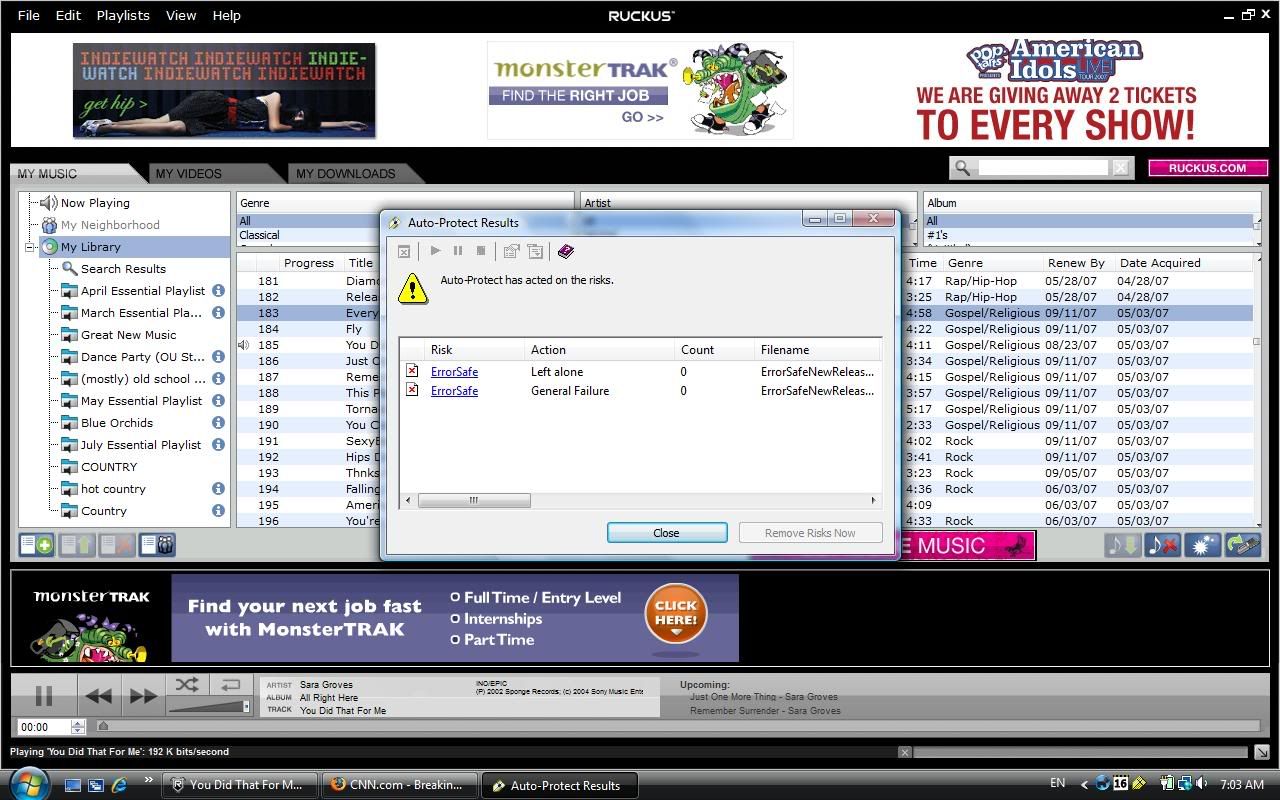
I've notified Ruckus about the advertisement, but it goes to show you the perils of 3rd-party ad networks. If you don't stay on top of the ads you're serving (or someone is serving on your behalf), something like this is bound to happen.
- David Oxley
UPDATE (8/17/07): Got hit with another redirect to errorsafe.com on Ruckus today, with two chief differences:
1) The product advertised was WinAntiVirus2007
2) The ad was Flash-based, and automatically opened the ErrorSafe page without any user interaction whatsoever.
Ugh. Ctl-Alt-Del, end-task iexplore.exe, and send Ruckus an e-mail (I've yet to hear back concerning my first experience...)
UPDATE #2 (8/17/07): Received a response from Ruckus saying that it's been cleaned. Likewise, see the comments for an apology from their senior director. I commend them on getting this taken care-of so quickly -- I'm not giving up my Ruckus anytime yet. :)
Labels: ads, errorsafe, ruckus, winfixer
posted by David @ 4:18 AM,
,
![]()
Ruckus Ads Get a Bit Too Much...
Sunday, August 05, 2007
First off, I love Ruckus. It's a free service that allows college students to download and listen to unlimited song tracks. The catch? All files are DRM-protected, time-limited (but are instantly renewed), and you have to suffer-through a single banner ad in the player. Big deal.
As we all know, though, banner ads can have their own issues. In the past, I have seen Ruckus ads try to run JavaScript, open new windows without user interaction, and run shady "You've Won -" offers. Ho-hum.
So what's new? Zango content. In particular, a steamy banner advertising:
"Anna Nicole Smith Lesbian Bathtub Sex Part I"
...classy. This is a new one to my knowledge -- porn offered by Ruckus ads?
The yieldmanager ad redirects to zango.com where, not surprisingly, the user is presented with thumbnails of several supposed porn movies featuring the late Anna Nicole Smith, with the caveat that an install of Zango's adware is in order. Being rather opposed to the stuff myself (both Zango and porn, that is), I let the ad recycle. H&R Block. That's respectable.
Needless to say, care is in order. I wouldn't be surprised to see a rogue AV scanner in there sooner than later, and sneaking IFRAMEs and exploits has been done with shady affiliate networks in the past...
- Nexus7
posted by David @ 1:47 PM,
,
![]()
A Little Phish-Finding
Wednesday, August 01, 2007
Well, I was bored. So what does an InfoSec student do when he's bored?
Hunt phishers, of course.
First, I headed over to SiteAdvisor to try and find an active phishing site. A Wells Fargo site is being hosted on a hacked immigration-support site:
hxxp://www.americanimmigrationnetwork.com/AAAA%20Kits/incudes/www.wellsfargo.com/wellsfargo/Updates_info/
Nothing special, mind you, just your standard hacking package. After a bit of fun with the source code and Tamper Data, I found the mailer, update.php. Unfortunately, all e-mailing is handled server-side (duh), so I had to try and find the uploaded PHP file. This was made *quite* easy by the hacker(s) leaving the entire uploaded kit, includes.zip, behind. Doh.
Upon extracting update.php, I found the following interesting bits:
1) A given author of "KELVINROLEX" Googling the name returns a Mobango account for a Nigerian man with the same handle. (NOTE: I am NOT saying that this is the same guy! There is no evidence of that whatsoever, save for what we know of Nigeria and scams...)
However, there *is* another link that I think is safe to assume our phisher is responsible for. Meet the "Kelvinrolex Php Mailer," a lame attempt at God-knows-what. It calls itself a "Spamer Inbox," but it seems to have no real functionality (and at version 1.5, no less). Whatever. Kelvin's phishing script isn't all that much more interesting...the guys uses Frontpage, for chrissake!
2) An e-mail addy: dv_max4009@yahoo.com
This little gem returns several hits on Google. Meet David Alvin Maxwell, a nice gent who spends his time defrauding women with romance scams. I guess the photos of legit models isn't all he's stealing these days...
3) A second e-mail address: lurdofhonor@gmail.com
No hits on Google, unfortunately.
Interesting part? Though Mr. Mobango is innocent until proven guilty, Mr. Maxwell is also from Nigeria. Hmmm.
Gotta love those anonymous Internets, waiting to be pillaged and plundered by techno-pirates such as KELVINROLEX and dv_max4009. Erm, Kelvin and David. From Nigeria. *grin*
- Nexus7
Labels: phishing
posted by David @ 6:57 PM,
,
![]()
Apple Just Got Pwned
Wednesday, May 30, 2007
...and I couldn't be happier.
Microsoft Surface is here.
Need I say more?
- David
Labels: microsoft
posted by David @ 6:37 AM,
,
![]()
It's Been a While
Sunday, May 20, 2007
I know my posts have been spotty at best -- alas, trying to keep two blogs updated is a pain-and-a-half, and thoughts of trying to consolidate them in some small way are definitely being considered. However, even when I'm not posting about malware, you can bet that I'm reading about it. Here's my Google Reader subscription list for malware blogs:
General and Misc. Malware/InfoSec:
Anti Rootkit Blog
Bits from Bill
C.I.S.R.T.
Dancho Danchev - Mind Streams of Information Security Knowledge
honeyblog
ReveNews: Revenue Sharing Opinions
SANS Internet Storm Center, InfoCON: green
Security Fix
SecurityFocus News
Sick of spam? Get mad and get even: Blog
Malware Fighters:
BenEdelman.org
Donna's SecurityFlash
Malware Advisor
Security Cadets
Security Garden
Spyware Sucks
The SpywareGuide Greynets Blog
Vitalsecurity.org - A Revolution is the Solution
wng's blog
Security Vendors:
Authentium Virus Blog
F-Secure Antivirus Research Weblog
F-Secure Linux weblog
Kasperky Lab Weblog
Panda Research
Security Response Weblog (Symantec)
Spybot-S&D news
SunbeltBLOG
A motley crew, but I feel that I get a good sense of current happenings in the malware-fighting world from them (not too many malware authors keep blogs that I know of...). Any glaring omissions I forgot or have yet to discover, or someone in there who shouldn't be?
- David
Labels: blogs
posted by David @ 6:14 AM,
,
![]()
Worms, Part 3
Sunday, April 22, 2007
So...looks like Mr. Rinbot has decided to release a new version of the beastie through computers already infected with the recent Rinbot.BC variant. Symantec is supposedly detecting this one as Rinbot.BF, though the variant mentioned in the write-up is NOT the same as the recent nasty, which runs from a file named "norantivirus.exe" in the Windows\System32 directory.
File name: norantivirus.exe
| File size: 252416 bytes |
| MD5: e0fd62d3d4c0258547690524563d8419 |
| SHA1: a63f017a3ab3405465ba90ba5377f30674aedbd3 |
| packers: EXECryptor |
| AhnLab-V3 | 2007.4.21.0 | 04.20.2007 | no virus found |
| AntiVir | 7.3.1.53 | 04.22.2007 | BDS/VanBot.CN |
| Authentium | 4.93.8 | 04.20.2007 | no virus found |
| Avast | 4.7.981.0 | 04.21.2007 | no virus found |
| AVG | 7.5.0.464 | 04.22.2007 | Win32/CryptExe |
| BitDefender | 7.2 | 04.22.2007 | no virus found |
| CAT-QuickHeal | 9.00 | 04.21.2007 | Backdoor.VanBot.cn |
| ClamAV | devel-20070416 | 04.23.2007 | no virus found |
| DrWeb | 4.33 | 04.22.2007 | BackDoor.IRC.Sdbot.1323 |
| eSafe | 7.0.15.0 | 04.22.2007 | Win32.VanBot.cn |
| eTrust-Vet | 30.7.3585 | 04.21.2007 | Win32/Nirbot.AZ |
| Ewido | 4.0 | 04.22.2007 | Backdoor.VanBot.cn |
| FileAdvisor | 1 | 04.23.2007 | no virus found |
| Fortinet | 2.85.0.0 | 04.23.2007 | W32/VanBot.BX!worm |
| F-Prot | 4.3.2.48 | 04.20.2007 | no virus found |
| F-Secure | 6.70.13030.0 | 04.23.2007 | Backdoor.Win32.VanBot.cn |
| Ikarus | T3.1.1.5 | 04.23.2007 | Backdoor.Win32.VanBot.cn |
| Kaspersky | 4.0.2.24 | 04.23.2007 | Backdoor.Win32.VanBot.cn |
| McAfee | 5014 | 04.20.2007 | W32/Nirbot.worm.gen |
| Microsoft | 1.2405 | 04.23.2007 | no virus found |
| NOD32v2 | 2210 | 04.22.2007 | no virus found |
| Norman | 5.80.02 | 04.21.2007 | W32/Malware.PXQ |
| Panda | 9.0.0.4 | 04.22.2007 | no virus found |
| Prevx1 | V2 | 04.23.2007 | Malware.Trojan.Backdoor.Gen |
| Sophos | 4.16.0 | 04.20.2007 | W32/ExDns-Fam |
| Sunbelt | 2.2.907.0 | 04.19.2007 | no virus found |
| Symantec | 10 | 04.23.2007 | W32.Rinbot.BF |
| TheHacker | 6.1.6.095 | 04.15.2007 | no virus found |
| VBA32 | 3.11.4 | 04.21.2007 | no virus found |
| VirusBuster | 4.3.7:9 | 04.22.2007 | no virus found |
| Webwasher-Gateway | 6.0.1 | 04.23.2007 | Trojan.VanBot.CN |
In addition, it was found active on a system running a vulnerable version of Symantec Client Security, but with NEW definitions loaded -- it was not detected upon a manual scan, either. Strange. Many of the vulnerable systems have already been exploited, cleaned, and patched with the BC run, though, so this one may have a harder time of things. Until there's a new 0-day to target, and there remains one dormant backdoored system on the network...
If nothing else, this is a reminder that a backdoor on a system is not just a risk for the user -- it's a backdoor into an entire network, and, conceivably, any and every computer on it.
- David
posted by David @ 7:23 PM,
,
![]()
